AISec 2017 Workshop: Modern Artificial Intelligence (AI) and Natural Language Processing (NLP) Techniques for Cyber Security
Saturday October 28, 2017 Centre for Excellence in Computational Engineering and Networking (CEN), Amrita Vishwa Vidyapeetham (Amrita University).
About Phase I of AISec 2017 Workshop series
The AISec (Artificial Intelligence for Cyber Security) group in the Computational Engineering and Networking (CEN) department at Amrita University is organizing a one-day workshop on 28th October, 2017. The workshop will cover Deep learning applications in the field of Cyber Security including NLP. The main aim of this workshop is to share the ideas of on-going research and exploratory topics, leading to possible collaborations between CEN faculty, Ph.D research scholars and students.
This is the era of data driven science. So to make sense of data is highly sought after skill in today’s massively connected data driven world. Machine learning brought a breakthrough in achieving this. Deep learning which is a subset of traditional AI and Machine learning techniques is the cutting edge technology in the current scenario. These set of techniques provides a platform for advanced decision making for complex problems. However these techniques are still in the Faraday stage in the field of Cyber Security. In turn it’s probably most helpful to think of deep learning as the cutting edge of cutting edge. As the size of data grows larger, deep learning play a key role in extracting knowledge, situational awareness, and security intelligence from Big Data. In order to take journey through deep learning to Big Data analytics, this workshop will help to initiate conversations.
The primary target audience of the workshop is BTech final year students, Mtech/M.Sc students, research scholars and faculty. We hope to have an interactive session, with a free exchange of ideas, views and comments. Please fill all the required details during registration. For more queries, please contact vinayakumarr77[at]gmail.com, barathiganesh.hb[at]gmail.com, **harikrishnannb07[at]]gmail.com **.
About AISec
AISec group at CEN understand the underlying mathematics knowledge required to apply Machine learning to Cyber Security tasks at Scale.
The ability to digitize our lives has outpaced our ability to stay safe. One of the biggest challenges is to understand the volume, velocity and complexity of threatening activity inside the network. We call this cyber intelligence. We have been developing a self-learning intelligence system by understanding the mathematics and using the most advanced machine learning technologies such as deep learning. A self-learning intelligence system learns a unique pattern of normal and abnormal activities of every device and user on a network, and correlates these insights in order to spot emerging threats that would otherwise go unnoticed. AISec group is fortunate to have Cyber Security experts and Researchers who have constantly smell the developments in Natural language processing, Image processing, Speech recognition and many other areas and incorporate those novel approaches to self-learning system to enhance the system detection rate of malicious activities. We are involved in developing large scale Security projects that involves Big-data Security Intelligence, Cyber-Physical systems security, Machine learning for Security, Complex Binary analysis, IoT, SCADA and Hardware security, Application & Network security, Advanced Forensics and Incident handling. Some of the tasks that we think and solve daily are to apply various Data mining, Machine learning and Deep learning approaches to various Cyber Security tasks such as Traffic Analysis, Intrusion detection, Malware Analysis, Botnet Analysis, Anonymity Services, Domain Generation Algorithms, Advanced mathematics to Crypto Systems.
Venue: CEN class room
[Registration is closed]
Recent Talks given by CEN faculties
Check out the earlier workshops conducted by CEN
Why we conduct workshop frequently? Advancement in technologies make many conventional engineering syllabus obselete
Program
09:30 - 11:15 Session 1: Basics of Optimization theory for Neural Networks
Presenter: Dr. Soman K. P.
Neural Networks (NNs) are one of the bedrock model on the area of Machine Learning and Artificial Intelligence. A numerical optimization problem appears when NNs are applied for solving Machine Learning problems, which consists in minimizing a non-convex function in a multidimensional space. Several algorithms based on the first order derivative (gradient type algorithms) of this non-convex function have been successfully applied for training Feedforward NNs (FNNs).
We begin with mathematical foundations of Neural networks. Convex and Non Convex Optimization - key theoretical principles, algorithms and applications will be discussed next. The Gradient Descent algorithm will be addressed. We culminate with the fascinating field of Machine Learning and Deep Learning- discussing key ideas and practical applications. A brief tour of the basics of Linear Algebra and Optimization will be covered as a part of the tutorial.
There has been a burst of recent research activity in all these areas. This workshop brings researchers from these vastly different domains and hopes to create a dialogue among them. In addition to the theoretical frameworks, the workshop will also feature practitioners, especially in the area of deep learning who are developing new methodologies for training large scale neural networks. The result will be a cross fertilization of ideas from diverse areas and school of thought.
11:15 - 11:30 Coffee Break
11:30 - 01:00 Session 2: Security Analytics: Big Data Analytics for Cyber Security
Presenter: Mr. Vijay Krishna Menon
01:00 - 02:00 Lunch
02:00 - 03:00 Session 3: AI (Data mining, Machine learning and Deep learning) techniques for CyberSecurity Use cases
03:00 - 08:00 Session 3.1: Hands-on Session
Presenter: Mr. Vinayakumar R, Mr. Barathi Ganesh HB and Mr. Harikrishnan N B
Funded Projects in CyberSecurity Domain
1. Information Security Assurance funded by Paramount computer systems - Principal investigator Dr. Soman KP.
2. Early Warning Framework Phase 2 - Network Security Situational Awareness and Countermeasures using DNS, BGP, Netflow and Remote Content Inception funded by DIETY, Govt. of India - Principal investigator Dr. Prabaharan Poornachandran, Co-PI Dr. Soman KP.
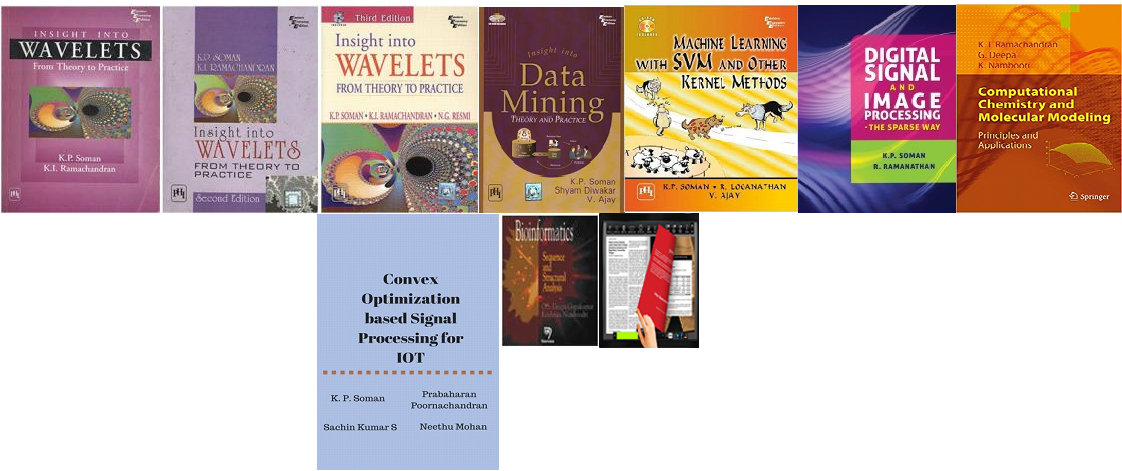
Books published from CEN on Signal processing and Machine learning
1. Dr. K.P. Soman, Prabaharan Poornachandran, Sachin Kumar S and Neethu Mohan, "Convex Optimization based Signal Processing for IOT." [Upcoming Book]
2. Dr. K.P. Soman and Dr. Ramachandran K.I, "Insight into Wavelets From Theory to Practice.", Prentice-Hall India 2004.
3. Dr. K.P. Soman, Shyam Diwakar, Ajay V., "Insight into Data Mining From Theory to Practice.", Prentice-Hall India, 2006.
4. Dr. K.P. Soman, Ajay. V, Loganathan R., "Machine Learning with SVM and other Kernel Methods.",Prentice-Hall India, 2009.
5. Dr. K.P.Soman, and Ramanthan, "Digital signal and Image Processing-The Sparse Way." Elsevier Publications, 2012.
6. Dr. Deepa G., Dr. Krishnan Namboodiri, "Bioinformatics: Sequential and Structural Analysis.", Narosa Publications.
7. Dr. K.I Ramachandran., Dr. Deepa, Dr. Krishnan Namboori, "Computational Chemistry and Molecular Modelling." -Springer international.
8. "Fractals for Everyone." [Online version](http://cen.amritafoss.org/downloads/) Manu Unni, Praveen Krishnan, Dr. K. P. Soman.